Encryption tools exist to protect your privacy… and also to make you feel like you’re an awesome spy. Today we’ll use a portable USB drive to hold all of
your passwords encrypted in a virtual disk hidden inside a file.
Certain kinds of cryptography were once called “weapons of mass destruction” because certain people thought it was so dangerous. Although clever people are making it good security more and more difficult, encryption tools like the one we’ll be using today are readily available, free, and provide a high level of
security that is nearly impossible to break into if done properly. Put on your spy mask and keep reading to find out how to build the perfect encrypted
password safe.
And for the skeptics that are curious about the “FBI” claim in our headline, you can read up on Operation Satyagraha, where money launderer Daniel Dantas has successfully encrypted his data and kept the FBI at bay for as long as a year with the very tools we’re going to use today.
your passwords encrypted in a virtual disk hidden inside a file.
Certain kinds of cryptography were once called “weapons of mass destruction” because certain people thought it was so dangerous. Although clever people are making it good security more and more difficult, encryption tools like the one we’ll be using today are readily available, free, and provide a high level of
security that is nearly impossible to break into if done properly. Put on your spy mask and keep reading to find out how to build the perfect encrypted
password safe.
And for the skeptics that are curious about the “FBI” claim in our headline, you can read up on Operation Satyagraha, where money launderer Daniel Dantas has successfully encrypted his data and kept the FBI at bay for as long as a year with the very tools we’re going to use today.
Step 1: Get A Reliable USB Drive
If you’re like many geeks, you’ve had your fair share of USB keydrives die on you. The cheap ten dollar drives may not be hardy enough to put a vault of your
most important passwords on, so you may have to get a little spendy and pick up one that will last for a while. How-to Geek doesn’t endorse any particular
brand of USB drives, but the author has had a lot of success with the Lacie Iamakey series. Lifehacker has featured them on several occasions, and they take a beating and keep your data safe. Use any brand that you think is good enough to hold keys to your online life—feel free to take the author’s
recommendation with all the grains of salt you see fit.
most important passwords on, so you may have to get a little spendy and pick up one that will last for a while. How-to Geek doesn’t endorse any particular
brand of USB drives, but the author has had a lot of success with the Lacie Iamakey series. Lifehacker has featured them on several occasions, and they take a beating and keep your data safe. Use any brand that you think is good enough to hold keys to your online life—feel free to take the author’s
recommendation with all the grains of salt you see fit.
Step 2: Create An Encrypted Drive or File with Truecrypt
A lot of software exists for encrypting files, but Truecrypt is a very solid choice. The two features we’re interested in are the ability to encrypt hidden files and the ability to run Truecrypt as portable software. You’ll need both if you ever intend to use your encrypted password key on any machine that isn’t your own.
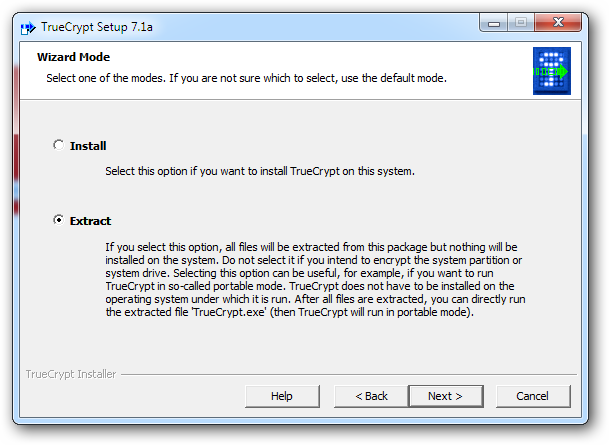
We’ve done several great guides on how to use TrueCrypt, so we’re not going to delve too deeply into the details today. Here we’ll go over our a basic
installation of a portable version of TrueCrypt on your USB disk. To begin, run the TrueCrypt installer and select “Extract” to install it on the USB disk.
And if you prefer, check out our previous guides to the program if you want to try and make your spy drive some other way.
installation of a portable version of TrueCrypt on your USB disk. To begin, run the TrueCrypt installer and select “Extract” to install it on the USB disk.
And if you prefer, check out our previous guides to the program if you want to try and make your spy drive some other way.
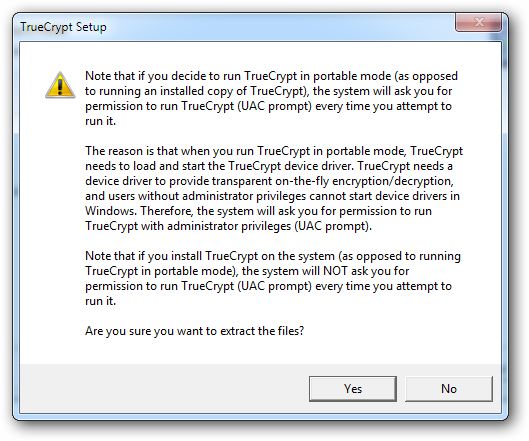
TrueCrypt can’t be used “transparently” as a portable EXE file. This basically means that you’ll need administrator control over a machine to use it as a
portable application. If this is okay to you, simply hit yes to go on to the next step. If not, you won’t really be able to open your encrypted drive on any machine but one with TrueCrypt installed, effectively tying it to your home PC. For today’s example, we’ll just be extracting it to the USB disk.
portable application. If this is okay to you, simply hit yes to go on to the next step. If not, you won’t really be able to open your encrypted drive on any machine but one with TrueCrypt installed, effectively tying it to your home PC. For today’s example, we’ll just be extracting it to the USB disk.
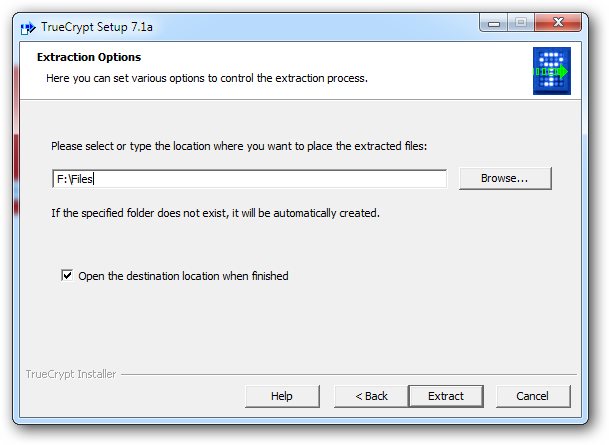
Extract the TrueCrypt files to any folder on the disk.
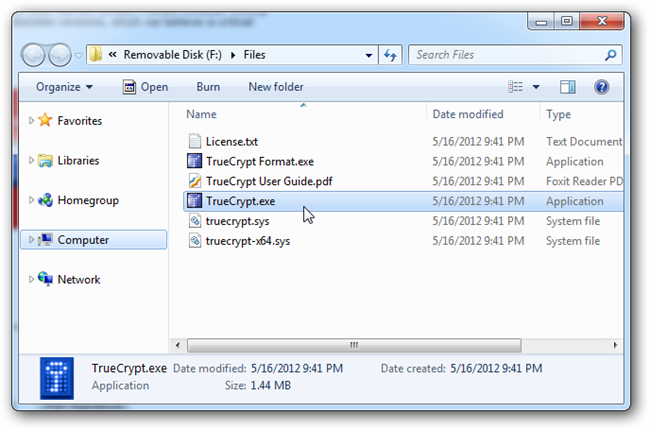
Find the TrueCrypt.exe file on your USB disk and run it. You’ll have to give that pesky administrator permission to start the program.
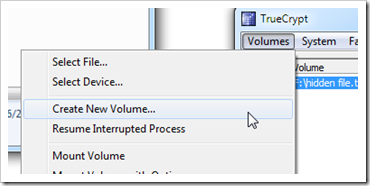
With TrueCrypt open, find “Create New Volume.”
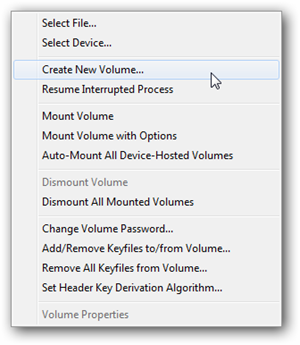
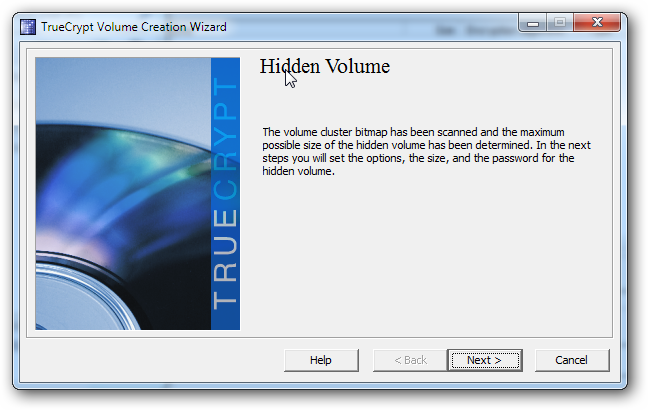
We’ll be creating a volume hidden inside a file. Again, since we’ve already covered it, we’re going to be brief. For a more detailed article on creating a
hidden volume with TrueCrypt (including how to create a hidden volume inside a hidden volume) check out our older article on hidden TrueCrypt volumes.
hidden volume with TrueCrypt (including how to create a hidden volume inside a hidden volume) check out our older article on hidden TrueCrypt volumes.
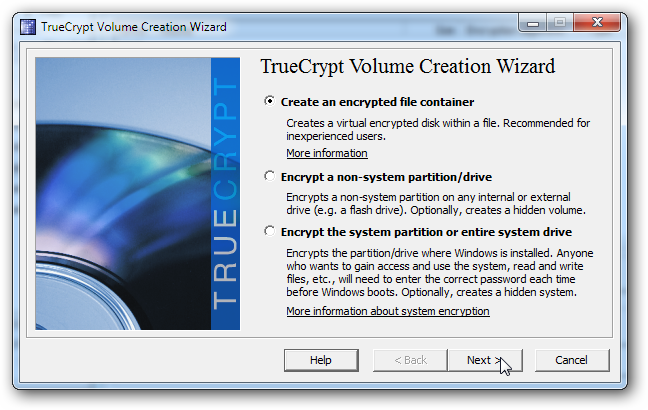
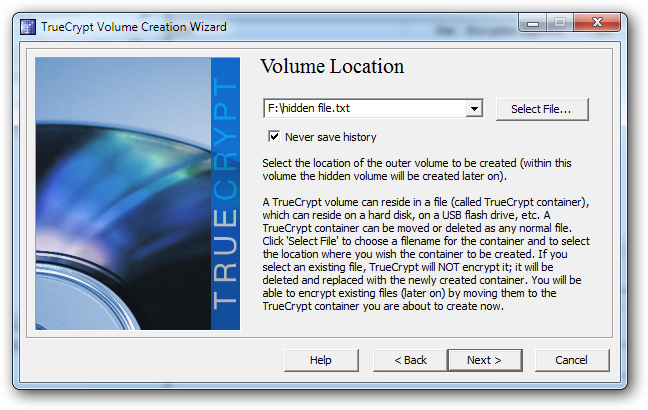
TrueCrypt asks us to pick a file to use as our hidden volume. Pick an empty, inconspicuous junk file. Don’t use anything important, because
this file will be overwritten with your encrypted volume once you’re done.
this file will be overwritten with your encrypted volume once you’re done.
With your volume file selected, click next to go onward.
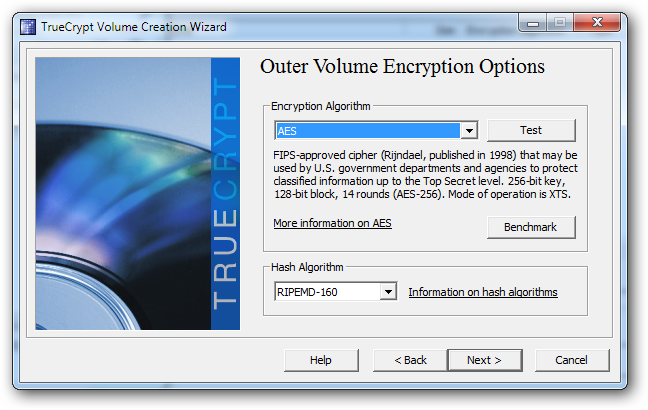
TrueCrypt supports lots of different Encryptions Algorithms, but the default one will work well enough. Research them all if you care to, or just use the
default AES encryption.
default AES encryption.
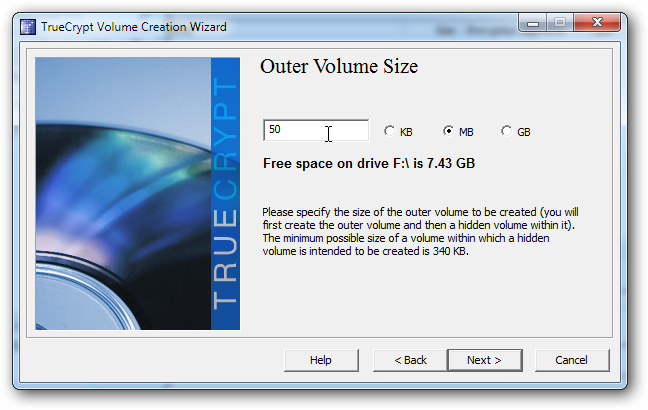
You’ll pick a size for your virtual disk. Unless your disk is full of big files, it might get noticed if it is too large. But don’t make it too small,
because you might not be able to fit the portable application in the virtual disk.
because you might not be able to fit the portable application in the virtual disk.
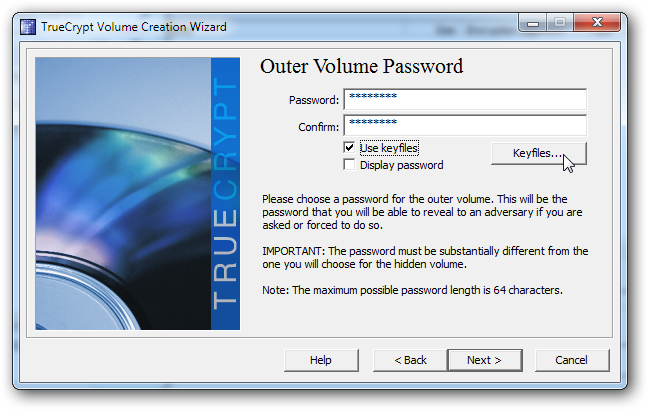
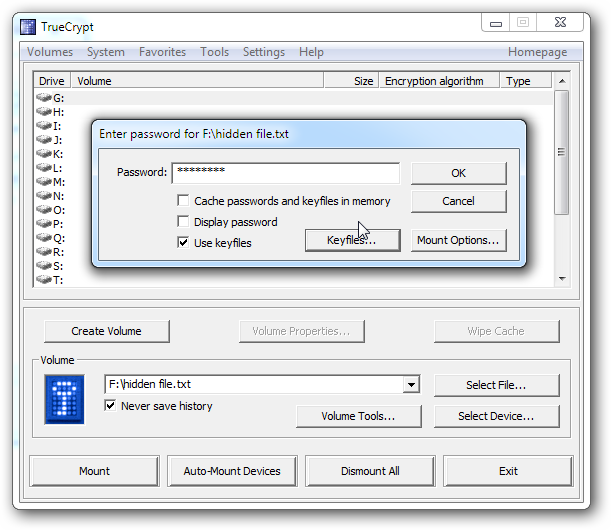
Once that’s done, input a password or passphrase and optional keyfiles. You should probably be able to remember any password, but it should be secure
enough that brute force methods of password cracking won’t break it easily.
enough that brute force methods of password cracking won’t break it easily.
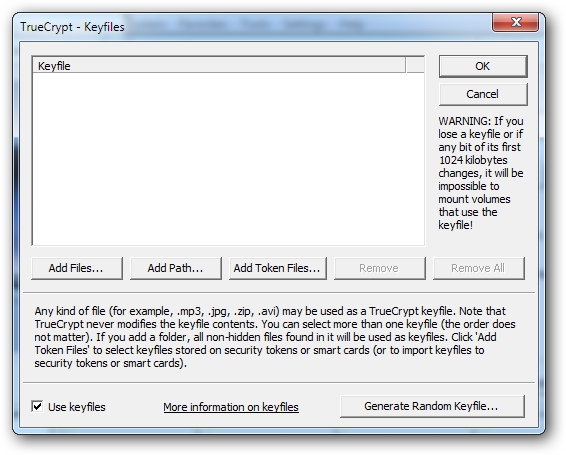
TrueCrypt (and KeePass as well) can use practically any kind of file as part of the password. This can add extra layers of security beyond any password to your
hidden volume. Simply be careful in your choice of file, since any change to the file’s contents may mean that it will no longer open your volume, and your
data may be lost forever. When you’re done picking (or not using) keyfiles, hit OK, then hit Next on the “Outer Volume” screen.
hidden volume. Simply be careful in your choice of file, since any change to the file’s contents may mean that it will no longer open your volume, and your
data may be lost forever. When you’re done picking (or not using) keyfiles, hit OK, then hit Next on the “Outer Volume” screen.
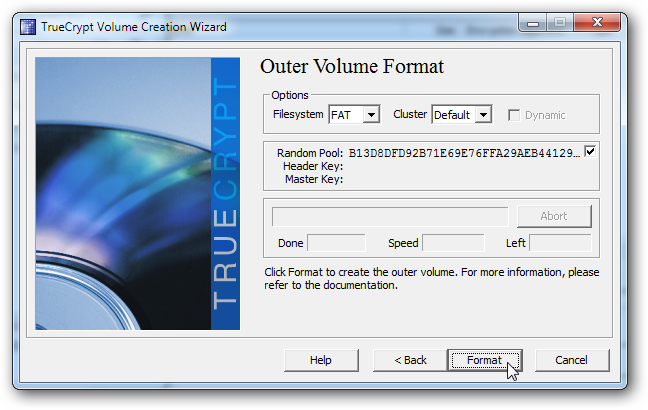
Click format when you’re done looking at the random strings generated by your mouse movements.
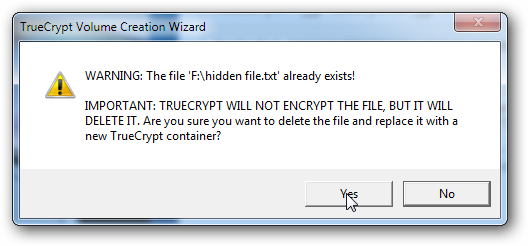
Last warning—you’re overwriting the file you picked. Make sure you don’t use one you intend to keep!
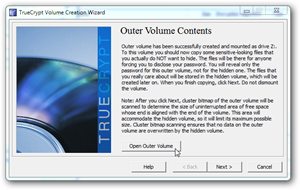
You can now mount your “outer volume” on this screen and go on to create a “hidden volume” if you wish.
It’s pretty easy and can provide yet another layer to your labyrinth of encryption. But for our demonstration today, we’ll be skipping this step and
mounting our drive to install KeePass.
mounting our drive to install KeePass.
Step 3: Mount the Hidden Drive and Install KeePass Portable
With TrueCrypt open, you can now open your hidden volume using your password and keyfile or keyfiles. Once you’ve mounted your virtual disk, you can open it by double clicking it in TrueCrypt.
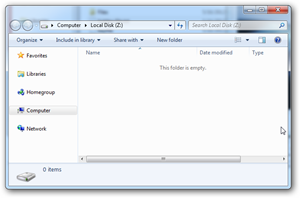
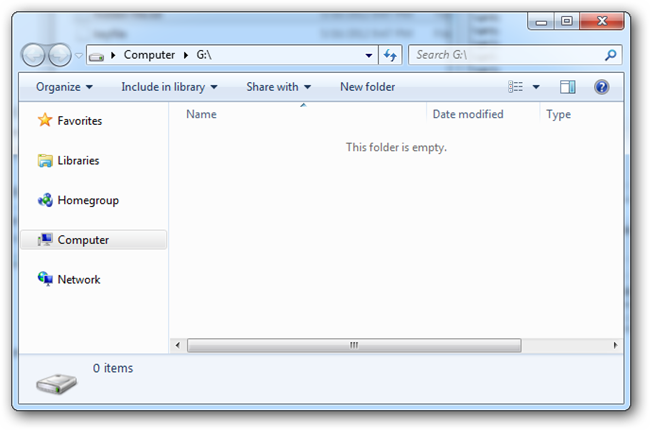
If you’re following along, you’ll find that your new virtual disk is empty.
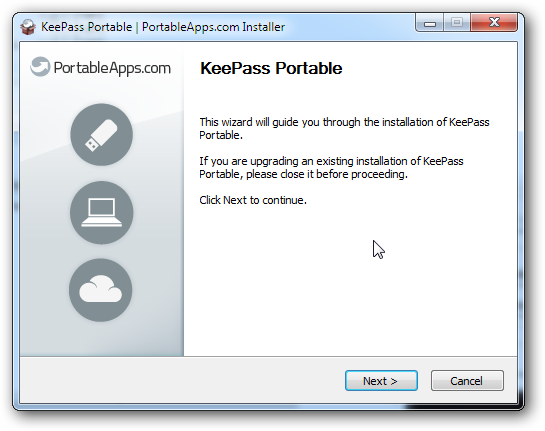
If you haven’t already, you can download KeePass portable to use on your new USB disk. You can download the standard version and only keep your passwords on the encrypted drive, but the portable version is also free and very easy to install on a USB disk.
Double click the installer to put the portable app on your (currently mounted) virtual disk.
In our example earlier, we mounted our encrypted disk as “G:” so we simply install KeePassPortable in that directory.
KeePass is a simple an intuitive program to use. It will generate and store long passwords as secure as we know how to make them. Even though the best
practice may be turning towards passphrases over passwords, KeePass will store any either kind and recall it for you whenever you need to break into your
accounts.
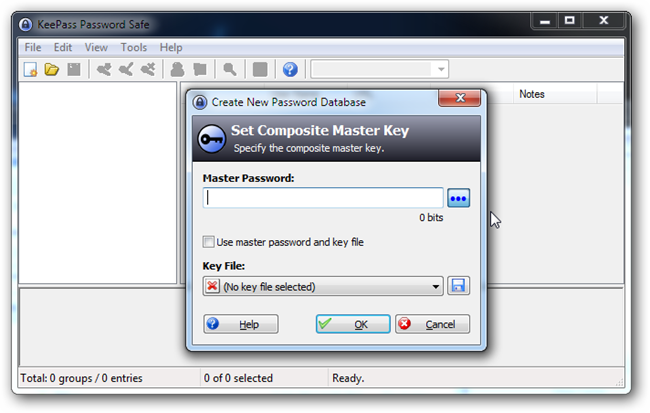
Assuming you’ve got the portable app installed, run it and select the option to create a new Password Database file. Like TrueCrypt, you can elect to use a
password and keyfile, recommended to add security beyond a simple password or phrase. Just remember, the same rule applies—don’t use a file that is likely to change, because you may lock yourself out of your password safe forever if it does.
practice may be turning towards passphrases over passwords, KeePass will store any either kind and recall it for you whenever you need to break into your
accounts.
Assuming you’ve got the portable app installed, run it and select the option to create a new Password Database file. Like TrueCrypt, you can elect to use a
password and keyfile, recommended to add security beyond a simple password or phrase. Just remember, the same rule applies—don’t use a file that is likely to change, because you may lock yourself out of your password safe forever if it does.
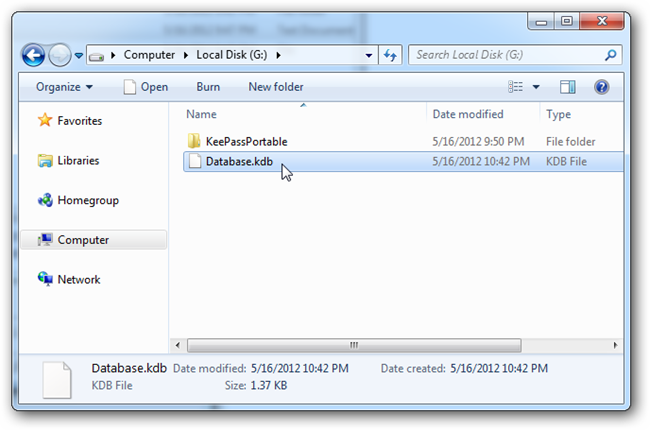
We won’t go into the wonders of KeePass today, since we’ve already covered them ages and ages ago and the program hasn’t functionally changed all that
much. But, once you’ve created your password database, save it to the encrypted drive (G:/ in our example) to keep it away from prying eyes.
For a more in-depth write up on KeePass, check out our previous write-up, with the basics and great tips on how to use it.
much. But, once you’ve created your password database, save it to the encrypted drive (G:/ in our example) to keep it away from prying eyes.
For a more in-depth write up on KeePass, check out our previous write-up, with the basics and great tips on how to use it.
Step 4: our Passwords are Now Safe From The KGB
Now that you’ve got your passwords locked away in an encrypted vault, you can rest assured they’re safe from all but the most insanely dedicated of users. So what else do you want to use your new cryptographic powers for? Sensitive, personal files can be stored here, and other portable apps can be installed in
your hidden virtual disk. Why not tell us about your experience with TrueCrypt in the comments, or simply email your thoughts to [email protected].
your hidden virtual disk. Why not tell us about your experience with TrueCrypt in the comments, or simply email your thoughts to [email protected].
Image Credits: Anonymity and the Internet by Stian Eikeland, Creative Commons. Spy by sewing punzie, Creative Commons.
Website Credits:
http://www.howtogeek.com/114155/how-to-hide-your-passwords-in-an-encrypted-drive-even-the-fbi-cant-get-into/
Website Credits:
http://www.howtogeek.com/114155/how-to-hide-your-passwords-in-an-encrypted-drive-even-the-fbi-cant-get-into/